Hi Everyone,
I’m working on a possibility for a parent to decide which child could push data to it - OpenMRS Issues
At this point, the parent needs to create an account with the access to certain endpoints. The child needs the credentials to this account in order to authenticate while pushing. The most common case is to create one account for all children. Please note that in this solution the parent does not track list of children with the access.
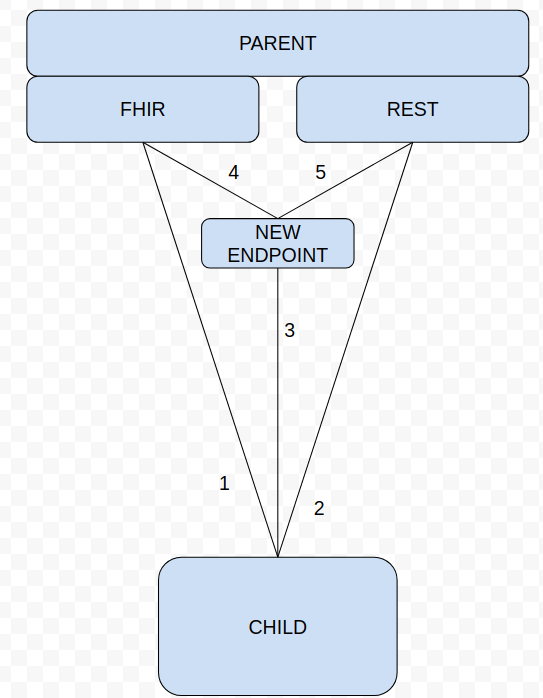
I want to add a whitelist of instances ids of children in the parent configuration, so it would be able to identify and verify children. I can easily add an instance id to messages sent by the child. Unfortunately, I cannot modify REST’s and FHIR’s endpoints, because validating instance ids is related to the SYNC2 module and users should be able to use FHIR and REST even when they do not need SYNC2.
Our solution is adding a separate controller for REST and FIHR in the SYNC2 module which will validate instance id, and then it will send the same message but with localhost instead of parent’s IP e.g. localhost/ws/rest/sync2/messages/261ce010-ade4-4a68-9ec6-15378c391f70 instead of 212.12.122.1/ws/rest/sync2/messages/261ce010-ade4-4a68-9ec6-15378c391f70 (the figure points: 3, 4 and 5).
FHIR’s and REST’s endpoints will not be removed because they have to be independent of the SYNC2 module (the figure points: 1 and 2). The security concerns are tackled by the user’s credentials, so the purpose of the whitelist is not to secure the parent, but to give it a possibility to cut off unnecessary requests.
Optionally the admin can go to […]/openmrs/admin/maintenance/settings.list?show=Webservices and set the ‘Rest Allowedips’ to localhost in order to disable these endpoints.
If you see any anomaly in this solution or you have any thoughts please let me know
Thanks in advance!