Hello there,
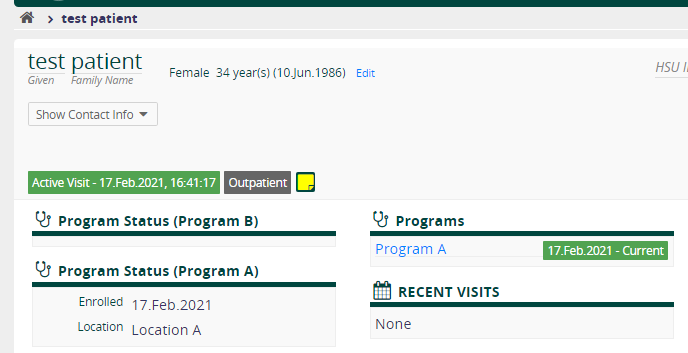
After making some tests with role System Developer (SUPERUSER), it was noticed that a user with this role cannot Enroll Patient in Program, cannot Edit and/or Delete patient enrollment. On the below image the buttons to enroll, edit and delete are missing:
After a little investigation on coreapps widgets controllers for program and programstatus, it seems there is a part of the code that is fetching current user privileges through openmrsREST to give, or not, privileges to these buttons on program and programstatus widgets. Check code here and here
When calling openmrsREST the response for this role (System Developer) is:
{
"sessionId": "3C1981EE238AB54D657923B4D13EFC3B",
"authenticated": true,
"user": {
"uuid": "5f1e7c8b-fdc1-447c-b0b8-efba5c97d72f",
"display": "dev_user",
"username": "dev_user",
"systemId": "215-4",
"userProperties": {
"loginAttempts": "0",
"emrapi.lastViewedPatientIds": "5687"
},
"person": {
"uuid": "7c6f1670-9588-45db-8ddf-506fa7e1afb7"
},
"privileges": [],
"roles": [
{
"uuid": "8d94f852-c2cc-11de-8d13-0010c6dffd0f",
"name": "System Developer"
}
]
},
"locale": "en_GB",
"allowedLocales": [
"en",
"es",
"fr",
"it",
"pt"
],
"sessionLocation": {
"uuid": "8fe901fb-4f09-466e-a7ea-dd95e0f3048d",
"display": "Location A",
"links": [
{
"rel": "self",
"uri": "http://localhost:8081/openmrs/ws/rest/v1/location/8fe901fb-4f09-466e-a7ea-dd95e0f3048d"
}
]
}
}
The privileges array is empty so conditions like the one below will never be true for this SUPERUSER.
if (response.user.privileges.some( (p) => { return p.name === 'Task: coreapps.enrollInProgram'; })) {
this.canEnrollInProgram = true;
};
Meaning that SUPERUSER can never enroll a patient.
This is happening also for relationships widget. Check code here .
What are your thoughts on this? Should we make a fix to ignore privileges if it’s superuser?
Thank you in advance for you feedback about this subject.
cc: @mksd @mogoodrich

 Thanks
Thanks