Hi all, Following the GSoC project Migrating from OpenMRS ID to a new SSO System we got urgent limitations.
The primary goal of the project was to integrate an identity provider with
-
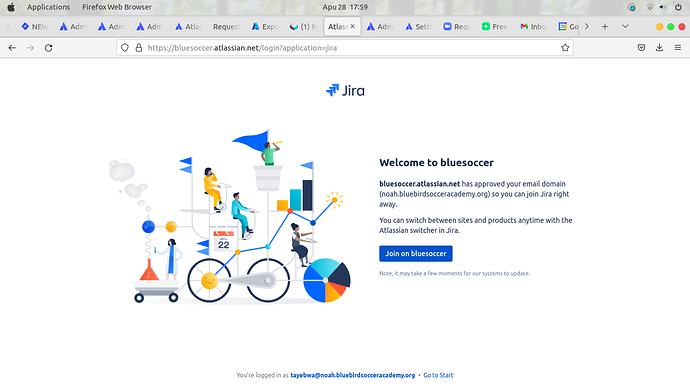
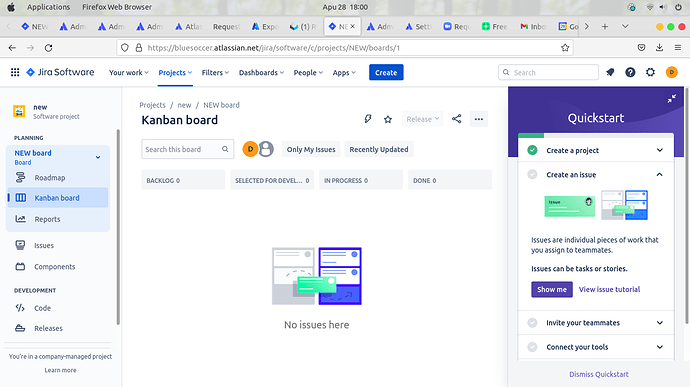
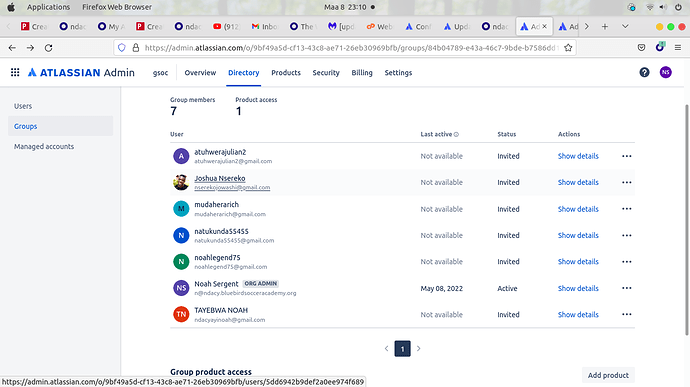
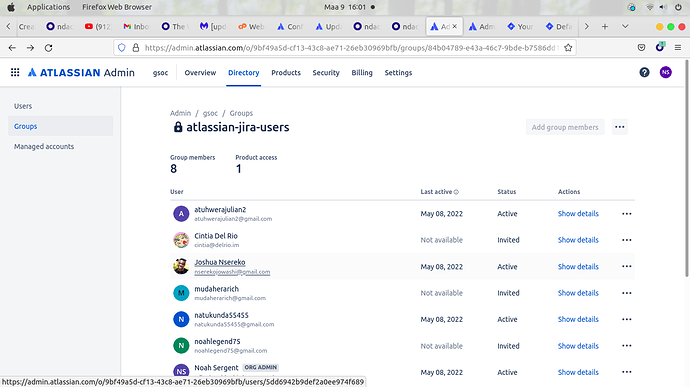
OpenMRS Atlassian cloud(jira and confluence)
-
OpenMRS discourse ie OpenMRS talk
The suggested idps were either Keycloak or Azure AD.
The limitations we may have as we plan to achieve the goals of our project
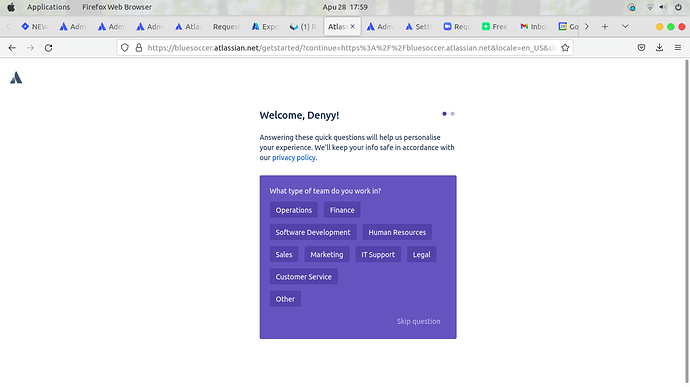
To integrate atlassian cloud with any Identity provider we need to use atassian access which is an organization-wide subscription that connects your Atlassian cloud products to your identity provider.
The following are limitations from atlassian access
-
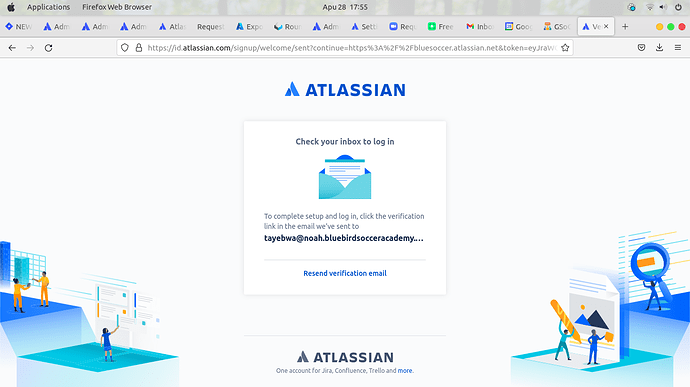
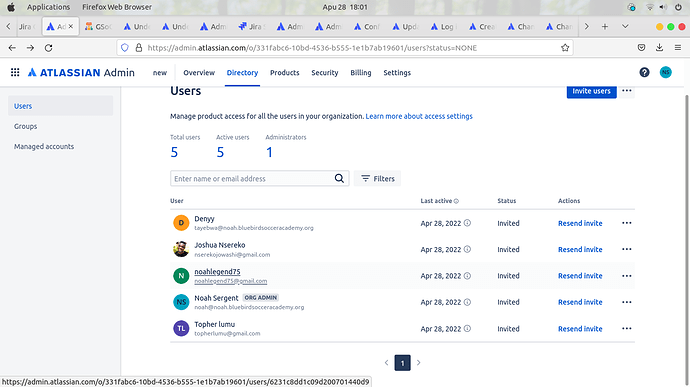
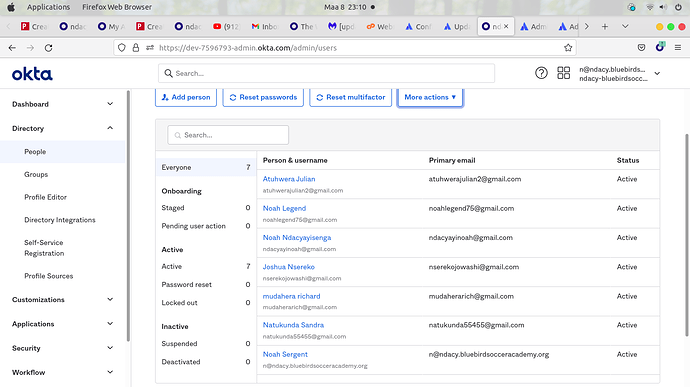
Atlassian Cloud only supports provisioning updates for users with verified domains. Changes made to users from a non-verified domain will not be pushed to Atlassian Cloud. Learn more about Atlassian verified domains [here]
-
Atlassian Cloud does not support group renames today. This means that any changes to the displayName of a group in Azure AD will not be updated and reflected in Atlassian Cloud.
-
The value of the mail user attribute in Azure AD is only populated if the user has a Microsoft Exchange Mailbox. If the user does not have one, it is recommended to map a different desired attribute to the emails attribute in Atlassian Cloud.
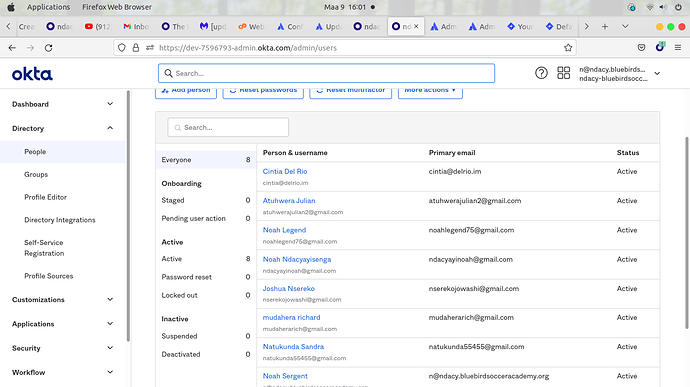
If OpenMRS is to use Atlassian cloud we need to have a verified domain/ verified domains and this won’t allow users to login from different mail domains ie @gmaill ,@yahoo, @hotmail among others which is quite inconveniencing.
Bullet No3 of the limitations
The value of the mail user attribute in Azure AD is only populated if the user has a Microsoft Exchange Mailbox. If the user does not have one, it is recommended to map a different desired attribute to the emails attribute in Atlassian Cloud.
What they are meaning here is domain mapping. This means we can use a broker to map many domains to atlassian cloud but these domains also have to be verified. Actually the best way I found understanding domain mapping in our case is using miniorange brokering. In that case miniorange acts as a broker to many different idps that handle different verified domains. something that can be found here What is Identity Brokering - miniOrange
Atlassian Access is the main culprit here which does not process any response (received either from miniOrange Broker or directly from IDP like Keycloak, Azure AD) for users with non-verified domains. All those solutions only work for the user with a verified domain.
So even if the miniOrange sends the user information to Atlassian Access for sync, Atlassian Access won’t process it.
Don’t know whether as OpenMRS we have a centralized domain probably @grace @jennifer @dkayiwa know better about this. This would mean that all users have to own mails of a verified domain.
The two solution my small eyes are seeing
-
- Getting a centralized domain where all user mails could spin from
-
- We host our own atlassian instances and we only change the idp since the idp looks to be the biggest problem. This solution doesn’t require a verified domain
Gathered this information while I was in sync with @cintiadr
cc @burke @grace @jennifer @herbert24 @kdaud @dkayiwa @ibacher @sharif