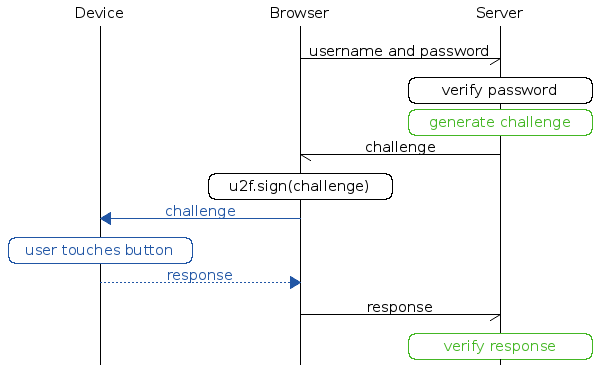
Bahmni using basic authentication (username, password) from OpenMRS so far. But always good to have additional security mechanism so that user is protected from fraudulent act. So, we are planning to introduce 2FA in Bahmni.
The following options are considered.
-
SMS verification (ex: OTP)
-
MDM (Mobile Device Management solutions)– no good open source solution available.
-
Giving the Android app administrator privileges – cannot do 2FA and also this will not be a generic approach because we may want to use 2FA from laptops as well.
The option chosen was SMS verification.
High level design:
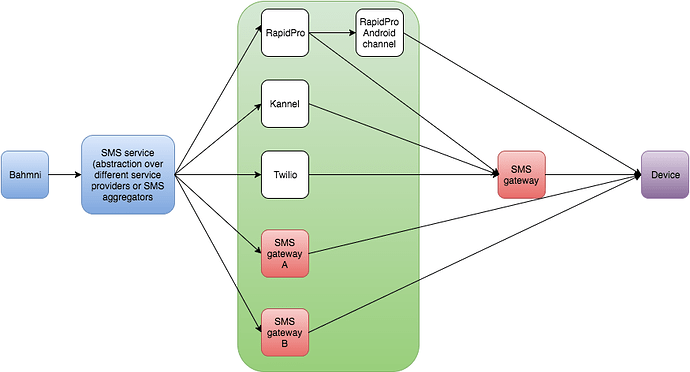
The high level view of the design looks as shown in the figure below. The idea is to provide an abstraction layer on top of different service providers (ex: Rapidpro, Twilio, Kannel) and SMS aggregators. This ensures that Bahmni talks to a single endpoint on the abstraction layer. This layers takes care of providing custom connectors to specific service providers or aggregators.
For heavily resource constrained settings where we cannot use aggregators, we can choose to use an Android phone to send SMS to the devices. One of the options of achieving this is to use Android Channel provided by RapidPro.
There was a OpenMRS talk about pluggable authentication. The current design proposal of OpenMRS is not using Spring Security. @angshuonline had a suggestion of using Spring Security to make the development more simpler. There was a design call with OpenMRS on this and notes can be found here.
Because of the timelines, we would not be going ahead with making changes in OpenMRS at this time. But, we will make necessary changes in Bahmni to realize this two-factor authentication.
We are happy to have suggestion on this and will try to fit it in current development or will schedule for near future.